Are you hacked off with boring magazine articles by halfwitted hacks about hacking hackers? Stories of viruses, ghosts in the machine, computer corruption? Well I am. So let’s all get a crinkly mouth together as I bring you my favourite true tales of computer clowns and the
This month MEL CROUCHER’s Monitor falls on that small part of society that hack into large mainframes, just for the sheer hell of it. Happy hackers or irresponsible idiots? Who cares? It’s all a bit of fun, innit?
Despite the hysterical media treatment of hackers leaving smutty messages on the Duke of Edinburgh’s bulletin board, despite the hundreds of thousands of quid spent prosecuting test cases like those against Steve Gold and Bob Schifreen, happy hackers do little or no material damage to anyone. Unlike the slimeballs who plant logic bombs and spread highly damaging viruses, or the software pirates who rip off everyone in sight, the happy hacker goes about his task for the sake of it, and no other, hidden motivation. In fact the motivation for these happy hackers is a bit like the reasons given by mountaineers and pot-holers. Computer security provides a sort of natural challenge against the individual that demands to be faced and overcome, for no other reason than the fact that it is there.
In the vast majority of happy hacking the culprit recognises an electronic challenge, accepts that challenge, and is content simply to break into that supposedly secure system — leaving only an amusing sign to prove his mission impossible accomplished. But sometimes the happy hacker does something a lot more spectacular.
John R MacDougall is something of a hero to many satellite movie watchers in America. They know him better as Captain Midnight, the first extra-terrestrial hacker in the world! MacDougall was a 25-year-old movie buff who worked part-time as an uplink operator at the Central Florida Teleport, the place where televised pap is beamed up to communication satellites. He also enjoyed watching the free entertainment supplied by the Galaxy 1 satellite’s Home Box Office channel. Well, that is he enjoyed it until Home Box Office decided to encode its signals and charge viewers $12.95 a month for a decoder.
Way back in the 1940s there was an American comic strip hero who went around righting wrongs without much regard to the letter of the law. He was called Captain Midnight, and as it happens John MacDougall rather liked the way this guy operated. At 12:32am on 27 April 1986, hacking history was made when the following message overrode Galaxy’s scheduled transmission due to the sheer power of its transmission signal, ‘Goodevening Home Box Office from Captain Midnight! $12.95 a Month? No Way! Showtime/Movie Channel Beware!’. Both federal and military authorities were severely shaken. If some bimbo could hijack a civilian satellite, what were the implications for national security, missile defences and porno-pix? (Cor, how can I get one of these satellite things? — Nick Roberts.) A massive hunt for Captain Midnight was launched. The search was on for someone with a minimum of a seven-metre satellite dish, a satellite uplink and an inability to spell ‘Good evening’. Things started to get very heavy when the Federal Communications Commission began to haul in suspects, left right and centre. Eventually MacDougall surrendered.
The authorities decided to make an example out of this outerspace hacker, and threw the book at the culprit, but as so often happens the whole thing has backfired. After the courts imposed a one year suspended jail sentence, and a five thousand dollar fine, Captain Midnight’s fans responded with messages of electronic support and cash. Our would-be superhero has since appeared in new comic strips all over the world, and the 1940s trash radio series from which he adopted his name has been dug out of the archives and is back on the air!
Most subscribers to the Radio Shack Bulletin Board System RBBS-PC in the Long Island, New York area were somewhat puzzled to find the following message balefully lurking on their screens in the early hours of 4 April 1985: ‘The secret is out, husband knows everything, quit town immediately, he’s armed and heading your way’. A significant percentage of subscribers, however, experienced a feeling considerably stronger than mere puzzlement. Convinced that only their most intimate pals had access to certain private areas of the network, they hurriedly packed their bags and headed for the hills. But what they should have done is waited until morning, when their screens displayed the follow-up message, ‘Arf! Arf! Got you, you dirty dog. The Recording Angel’. (Har Har, very funny — Ed.)
At 9:14pm on Sunday 22 November 1987, during Chicago’s Channel 9 sports bulletin, the computer controlling the broadcast waves suffered a severe bout of piracy. Which is to say Chicago Headroom made his first live TV appearance. Chicago Headroom appears to be a young guy with a spotty bum, sporting a Max Headroom mask, with electronic zigzag patterns behind him. How do we know he’s got a spotty bum? I’ll tell you later. Most of the city’s television stations have their transmitters tacked on the sides of the Sears Tower and the John Hancock building, the tallest structures in the State. Studio and outside broadcast signals are beamed to these transmitters using line-of-sight microwaves, and the cops know exactly where Chicago Max operates from, having plotted straight lines on a map from the studios to the intersection points of the microwaves... somewhere near 2501 West Bradley Place. The trouble is they ain’t dealing with a naughty schoolkid, but a very sophisticated and wealthy joker.
Apparently Chicago Max has got the power to override the genuine TV shows with some expert knowledge and a microwave transmitter costing upwards of $25000, probably operating from a Minicam studio truck! He often breaks into radio programmes and so far he has appeared on any TV channel he chooses. Last time out, he decided to treat his startled audience to a programme showing the usual electronic backdrop plus his bare arse being spanked with a fly swatter. The broadcast quality was so good that one viewer offered to help cure the 17 zits (how can you be so sure about the number, Mel? — Ed) which made a special guest appearance. The FBI, on the other hand, have offered a $10000 fine and a year in jail!
When the LA Police eventually arrested the notorious criminals who had sprinkled filth, smut, obscenity and mayhem throughout the city’s electronic mailing system, they had something of a surprise. The Computer Access Gang consisted of a young lady, two small children and mild-mannered Lewis de Payne. Their motivation, they confessed, was ‘a sense of pride to be able to show each other we could crack any security code of a computer’. What had puzzled computer experts was how the hell the gang had worked out what passwords to use. As the dirty words continued invading their files these experts spent thousands of dollars trying to plug gaps and change security systems. Perhaps one of them goes golfing with the judge because they certainly got their vengeance — Lewis de Payne got sent down for six months porridge. This strikes me as a wee bit unfair, especially when his amazingly sophisticated method of code-cracking came out at the trial. All he did, it seems, was to phone up a member of staff at the victim’s office, tell them that he was the program maintenance man, and ask them! Nobody ever challenged him.
Certain members of the staff at Dixons were pleasantly relieved from the usual tedium of those dreadful video promos, which repeat adverts ad nauseam to shoppers and workers alike, thanks to the efforts of Mr Dean Talboys. Up before the beak, Dean described his creative hacking as ‘a little prank’, but Acton Crown Court didn’t see the joke and ordered him to pay a thousand quid for criminal damage compensation. His tampering with the Dixons shops group computer system got somewhat out of control, and mutated to such an extent that it fouled up the entire system, finally displaying the ironically appropriate message: ‘Goodbye Folks!’.
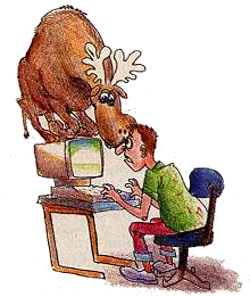
Mark Berkowitz is a technician working on the United States Space Programme. He’s got a PC at home for electronic mail, and he’s gone and rigged it up to a speech synthesiser, cos he’s that kind of guy. One night last year he was sitting in his den when a metallic voice said, ‘Hey man! What the hell are you doing?’. As he dropped his book along with his jaw, the computerised image of a bull moose poked its head round the side of his screen, walked across to the other side, evacuated its bowels and disappeared. Over a year later, Mark now sits in front of his screen, obsessed and waiting for the moose’s second coming (not to mention going). He’s still waiting. (Cancel my trip on the Space Shuttle — Ed.)

Easily the most spectacular computer hack of all time was perpetrated by Germans, the incredible Chaos Computer Club of Hamburg. Their logic tends to amuse or terrify, depending on whether or not you find the prospect of computers controlling World War III reassuring or farcical. Chaos reckoned that the computers were much too dangerous a tool to be left under the control of politicians and the military, so they hacked into the National Aeronautics and Space Administration network. (Yes, that’s NASA!) They then installed ‘Trojan Horses’ in 135 computers in the network, located in remote regions of the planet as well as in the USA, Britain, France, Switzerland and Japan. The Chaos Computer Club thought that they would allow themselves a back door into the NASA fortress just to keep an eye on the ‘East-West conflict, economic crime, industrial espionage and the legitimate security interest of high-tech institutions’. Personally, I find this not only very funny, but also reassuring, because it proves yet again that there is no such thing as computer security, All the time there is a chance for terrorists and loonies to get into the system there’s a chance computers will go as haywire as the Mark Berkowitz example.
Fortunately the military so far refuse to surrender their human chain of command to machines, and with humans involved there is always a chance to question or refuse an order — with machines, there ain’t. But let me end this piece with a recent document intended to catch happy hackers.
Gerald W Grindler is corporate computer security manager at Southwestern Bell Telephone, in St Louis. He’s the guy who’s advising parents on how to tell if their criminal offspring are hacking away, and this is some of his advice. Grindler suggests that parents should learn some computer jargon and eavesdrop on the kiddiewinkies to see if they use words like ‘bulletin board’ and ‘access code’. (Cripes, that should work!) They should also check their phone bills and review long-distance telephone charges. (If the kids are using a Blue Box they might just forget to call the kiddy cops, freephone calls are very attractive, even to adults!) In other words, even the experts are piddling in the wind, totally out of touch with the fact that networked computer security is a contradiction in terms. And all the time that the happy hackers prove electronic security systems to be useless, by means of expert knowledge and a large dose of humour, I for one applaud them.